Election Management Software
Electionware®
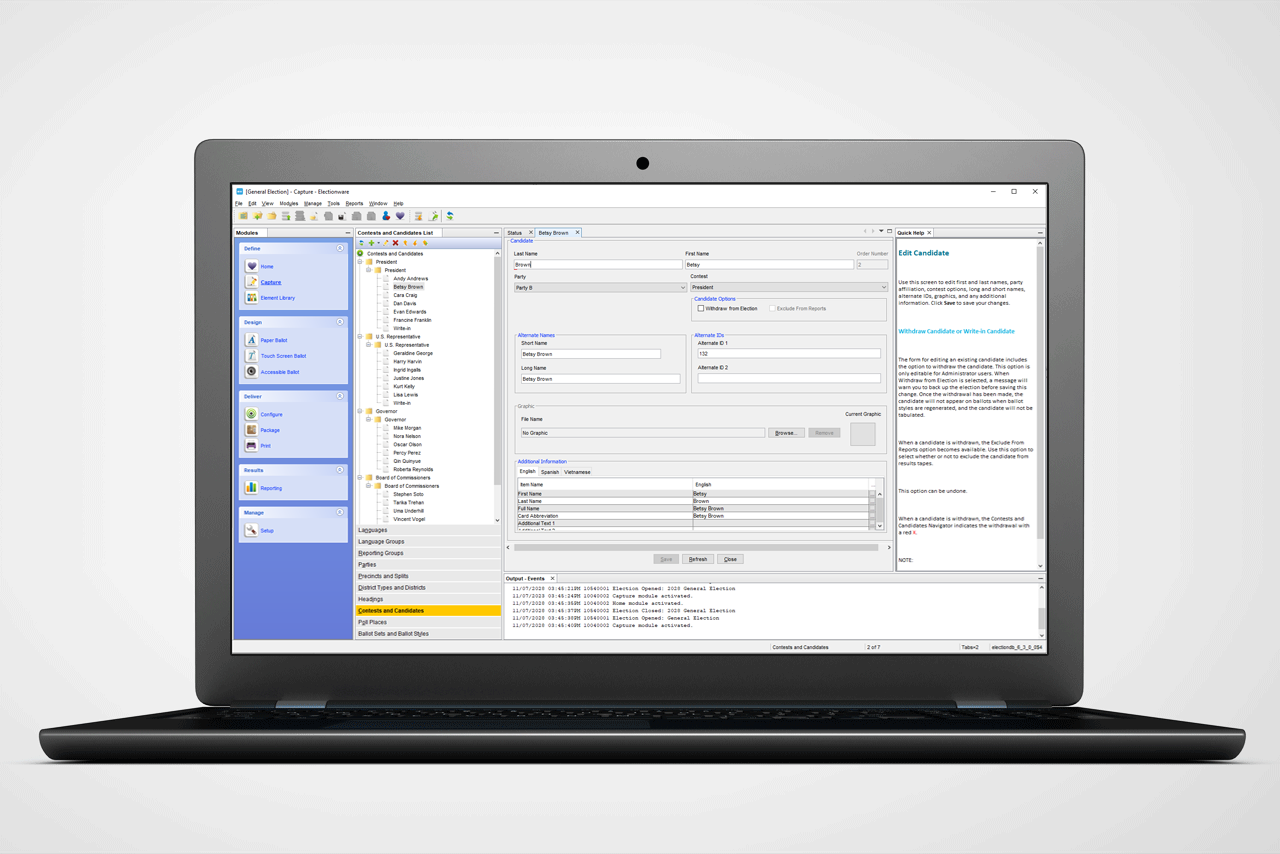
Electionware election management software allows jurisdictions of all sizes to manage their elections through the software’s easy-to-understand, user-friendly interface.
Security features:
- Physical and system access controls
- Audit logs
- Proprietary flash drives
- System application controls
- Encryption, hash validation and digital signature
Easy to master
Jurisdictions of all sizes can manage their elections through Electionware’s easy-to-understand, user-friendly interface. Users find the software easy to navigate because its design is based on actual election workflow. The software accommodates early and overseas voting, Americans with Disabilities Act compliance, ballot adjudication and write-in support, and election night reporting.
What’s in it for election officials?
Intelligence
Real-time election data queries and reports; workflow management and error alerts; enforced data accuracy; user customization; tracking of election media; helpful status indicators for incoming results.
Productivity
Fast data import; reuse of election and ballot layout templates; simple translation and audio file management; multiple simultaneous users; ballot image filtering, viewing and printing.
Power
Management of thousands of ballot styles and precincts; incorporation of many languages; deployment of multiple levels of security.
Built for election management
Work simultaneously
Electionware’s multiuser functionality allows multiple authorized election personnel on a closed-network system to prepare precinct flash drives simultaneously or load results while running reports, even on different elections.
Ensure electionwide uniformity and compliance
Electionware uses one database to support multiple equipment types, manages nearly 15,000 ballot styles and just under 10,000 precincts, and supports numerous languages. The software also contains and deploys multiple levels of security configurable to jurisdiction requirements.
5 comprehensive election management
software groups
Electionware gives election administrators the software tools needed to:
- Create elections
- Design ballots
- Configure digital tabulation and accessible equipment
- Manage election results data
- Generate custom results reports
These tasks are coordinated through Electionware’s five software groups, each representing a stage of the election process.
Each group includes modules that handle specific functions for setting up an election and processing results — all of which can be configured.
| Group | Features |
|---|---|
Manage |
|
Define |
|
Design |
|
Deliver |
|
Results |
|
Security you can count on.®
System security
- The Election Management System (EMS) running Electionware is a hardened server, configured to include only the services, applications, utilities and settings required to successfully operate the system. The hardening process turns the server into a single-purpose device, dedicated solely to creating and operating elections.
- Electionware is protected by multifactor authentication using Windows BitLocker.
- Electionware requires usernames and passwords to launch the EMS application. The restricted user roles determine which features are accessible.
- The database server accesses data through a dedicated hardened EMS client on an air-gapped monitored network.
Physical access controls
- Officials are required to implement a strong physical and procedural security plan that limits access to Electionware to authorized personnel only.
Audit logs
- Electionware maintains an audit log that tracks and saves a record of all system processes and user actions with usernames. This audit log can be filtered by date and type of event.
- The log can be printed or saved in a variety of file formats, including PDF, RTF, HTML, XLSX and CSV. The log operates during all processes, including results processing. Optionally, log events can be viewed in real time in the output window, which displays errors in red text, warnings in blue text and normal events in black text.
- Audit records created during election definition and ballot preparation include records for all steps in the finalization of the ballot layout. These records are date- and time-stamped and include a description of the action and the module in which the action occurred. Audit reports can be filtered by date or event type and can be sorted by ascending or descending time stamps.
- Audit logs on the EMS server, either in Electionware or the database, cannot be modified.
Need more information?
That’s why we’re here. The dedicated ES&S representative for your state can help you determine the best solutions for your jurisdiction.